The Open System Interconnection Reference Model (OSI Reference Model or OSI Model) is an abstract description for layered communications and computer network protocol design. It was developed as part of the Open Systems Interconnection (OSI) initiative.[1] In its most basic form, it divides network architecture into seven layers which, from top to bottom, are the Application, Presentation, Session, Transport, Network, Data-Link, and Physical Layers. It is therefore often referred to as the OSI Seven Layer Model.
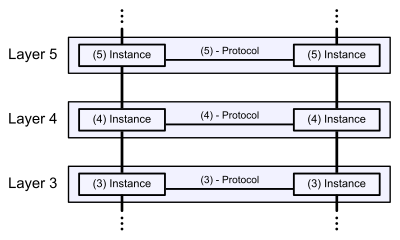
A layer is a collection of conceptually similar functions that provide services to the layer above it and receives service from the layer below it. On each layer an instance provides services to the instances at the layer above and requests service from the layer below. For example, a layer that provides error-free communications across a network provides the path needed by applications above it, while it calls the next lower layer to send and receive packets that make up the contents of the path. Conceptually two instances at one layer are connected by a horizontal protocol connection on that layer.
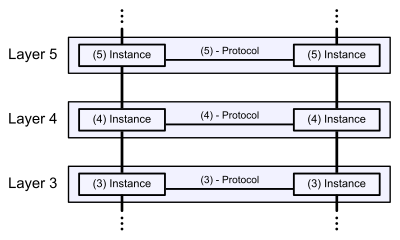
Communication in the OSI-Model (Example with layers 3 to 5)
[edit]History
In 1970, work on a layered model of network architecture was started and the International Organization for Standardization (ISO) began to develop its OSI framework architecture. OSI has two major components: an abstract model of networking, called the Basic Reference Model or seven-layer model, and a set of specific protocols.
Note: The standard documents that describe the OSI model can be freely downloaded from the ITU-T as the X.200-series of recommendations.[2] A number of the protocol specifications are also available as part of the ITU-T X series. The equivalent ISO and ISO/IEC standards for the OSI model are available from ISO, but only some of them at no charge.[3]
All aspects of OSI design evolved from experiences with the CYCLADES network, which also influenced Internet design. The new design was documented in ISO 7498 and its various addenda. In this model, a networking system is divided into layers. Within each layer, one or more entities implement its functionality. Each entity interacts directly only with the layer immediately beneath it, and provides facilities for use by the layer above it.
Protocols enable an entity in one host to interact with a corresponding entity at the same layer in another host. Service definitions abstractly describe the functionality provided to an (N)-layer by an (N-1) layer, where N is one of the seven layers of protocols operating in the local host.
[edit]Description of OSI layers
[edit]Layer 1: Physical Layer
Main article:
Physical LayerThe Physical Layer defines the electrical and physical specifications for devices. In particular, it defines the relationship between a device and a physical medium. This includes the layout of pins, voltages, cablespecifications, hubs, repeaters, network adapters, host bus adapters(HBAs used in storage area networks) and more.
To understand the function of the Physical Layer in contrast to the functions of the Data Link Layer, think of the Physical Layer as concerned primarily with the interaction of a single device with a medium, where the Data Link Layer is concerned more with the interactions of multiple devices (i.e., at least two) with a shared medium. The Physical Layer will tell one device how to transmit to the medium, and another device how to receive from it (in most cases it does not tell the device how to connect to the medium). Standards such as RS-232 do use physical wires to control access to the medium.
The major functions and services performed by the Physical Layer are:
Parallel SCSI buses operate in this layer, although it must be remembered that the logical SCSI protocol is a Transport Layer protocol that runs over this bus. Various Physical Layer Ethernet standards are also in this layer; Ethernet incorporates both this layer and the Data Link Layer. The same applies to other local-area networks, such as token ring, FDDI, ITU-T G.hn and IEEE 802.11, as well as personal area networks such as Bluetooth and IEEE 802.15.4.
[edit]Layer 2: Data Link Layer
The Data Link Layer provides the functional and procedural means to transfer data between network entities and to detect and possibly correct errors that may occur in the Physical Layer. Originally, this layer was intended for point-to-point and point-to-multipoint media, characteristic of wide area media in the telephone system. Local area network architecture, which included broadcast-capable multiaccess media, was developed independently of the ISO work in IEEE Project 802. IEEE work assumed sublayering and management functions not required for WAN use. In modern practice, only error detection, not flow control using sliding window, is present in data link protocols such as Point-to-Point Protocol (PPP), and, on local area networks, the IEEE 802.2 LLC layer is not used for most protocols on the Ethernet, and on other local area networks, its flow control and acknowledgment mechanisms are rarely used. Sliding window flow control and acknowledgment is used at the Transport Layer by protocols such as TCP, but is still used in niches where X.25 offers performance advantages.
The ITU-T G.hn standard, which provides high-speed local area networking over existing wires (power lines, phone lines and coaxial cables), includes a complete Data Link Layer which provides both error correction and flow control by means of a selective repeat Sliding Window Protocol.
Both WAN and LAN services arrange bits, from the Physical Layer, into logical sequences called frames. Not all Physical Layer bits necessarily go into frames, as some of these bits are purely intended for Physical Layer functions. For example, every fifth bit of the FDDI bit stream is not used by the Layer.
[edit]WAN Protocol architecture
Connection-oriented WAN data link protocols, in addition to framing, detect and may correct errors. They are also capable of controlling the rate of transmission. A WAN Data Link Layer might implement a sliding window flow control and acknowledgment mechanism to provide reliable delivery of frames; that is the case for SDLC and HDLC, and derivatives of HDLC such as LAPB and LAPD.
[edit]IEEE 802 LAN architecture
Practical, connectionless LANs began with the pre-IEEE Ethernet specification, which is the ancestor of IEEE 802.3. This layer manages the interaction of devices with a shared medium, which is the function of a Media Access Control sublayer. Above this MAC sublayer is the media-independent IEEE 802.2 Logical Link Control (LLC) sublayer, which deals with addressing and multiplexing on multiaccess media.
While IEEE 802.3 is the dominant wired LAN protocol and IEEE 802.11 the wireless LAN protocol, obsolescent MAC layers include Token Ringand FDDI. The MAC sublayer detects but does not correct errors.
[edit]Layer 3: Network Layer
Main article:
Network LayerThe Network Layer provides the functional and procedural means of transferring variable length data sequences from a source to a destination via one or more networks, while maintaining the quality of service requested by the Transport Layer. The Network Layer performs networkrouting functions, and might also perform fragmentation and reassembly, and report delivery errors. Routers operate at this layer—sending data throughout the extended network and making the Internet possible. This is a logical addressing scheme – values are chosen by the network engineer. The addressing scheme is hierarchical.
The best-known example of a Layer 3 protocol is the Internet Protocol (IP). It manages the connectionless transfer of data one hop at a time, from end system to ingress router, router to router, and from egress router to destination end system. It is not responsible for reliable delivery to a next hop, but only for the detection of errored packets so they may be discarded. When the medium of the next hop cannot accept a packet in its current length, IP is responsible for fragmenting the packet into sufficiently small packets that the medium can accept.
A number of layer management protocols, a function defined in the Management Annex, ISO 7498/4, belong to the Network Layer. These include routing protocols, multicast group management, Network Layer information and error, and Network Layer address assignment. It is the function of the payload that makes these belong to the Network Layer, not the protocol that carries them.
[edit]Layer 4: Transport Layer
The Transport Layer provides transparent transfer of data between end users, providing reliable data transfer services to the upper layers. The Transport Layer controls the reliability of a given link through flow control, segmentation/desegmentation, and error control. Some protocols are state and connection oriented. This means that the Transport Layer can keep track of the segments and retransmit those that fail.
Although not developed under the OSI Reference Model and not strictly conforming to the OSI definition of the Transport Layer, typical examples of Layer 4 are the Transmission Control Protocol (TCP) and User Datagram Protocol (UDP).
Of the actual OSI protocols, there are five classes of connection-mode transport protocols ranging from class 0 (which is also known as TP0 and provides the least error recovery) to class 4 (TP4, designed for less reliable networks, similar to the Internet). Class 0 contains no error recovery, and was designed for use on network layers that provide error-free connections. Class 4 is closest to TCP, although TCP contains functions, such as the graceful close, which OSI assigns to the Session Layer. Also, all OSI TP connection-mode protocol classes provide expedited data and preservation of record boundaries, both of which TCP is incapable. Detailed characteristics of TP0-4 classes are shown in the following table:[4]
| Feature Name | TP0 | TP1 | TP2 | TP3 | TP4 |
|---|
| Connection oriented network | Yes | Yes | Yes | Yes | Yes |
| Connectionless network | No | No | No | No | Yes |
| Concatenation and separation | No | Yes | Yes | Yes | Yes |
| Segmentation and reassembly | Yes | Yes | Yes | Yes | Yes |
| Error Recovery | No | Yes | No | Yes | Yes |
| Reinitiate connection (if an excessive number of PDUs are unacknowledged) | No | Yes | No | Yes | No |
| multiplexing and demultiplexing over a single virtual circuit | No | No | Yes | Yes | Yes |
| Explicit flow control | No | No | Yes | Yes | Yes |
| Retransmission on timeout | No | No | No | No | Yes |
| Reliable Transport Service | No | Yes | No | Yes | Yes |
Perhaps an easy way to visualize the Transport Layer is to compare it with a Post Office, which deals with the dispatch and classification of mail and parcels sent. Do remember, however, that a post office manages the outer envelope of mail. Higher layers may have the equivalent of double envelopes, such as cryptographic presentation services that can be read by the addressee only. Roughly speaking, tunneling protocolsoperate at the Transport Layer, such as carrying non-IP protocols such as IBM's SNA or Novell's IPX over an IP network, or end-to-end encryption with IPsec. While Generic Routing Encapsulation (GRE) might seem to be a Network Layer protocol, if the encapsulation of the payload takes place only at endpoint, GRE becomes closer to a transport protocol that uses IP headers but contains complete frames or packets to deliver to an endpoint. L2TP carries PPP frames inside transport packet.
[edit]Layer 5: Session Layer
Main article:
Session LayerThe Session Layer controls the dialogues (connections) between computers. It establishes, manages and terminates the connections between the local and remote application. It provides for full-duplex, half-duplex, or simplex operation, and establishes checkpointing, adjournment, termination, and restart procedures. The OSI model made this layer responsible for graceful close of sessions, which is a property of theTransmission Control Protocol, and also for session checkpointing and recovery, which is not usually used in the Internet Protocol Suite. The Session Layer is commonly implemented explicitly in application environments that use remote procedure calls.
[edit]Layer 6: Presentation Layer
The Presentation Layer establishes a context between Application Layer entities, in which the higher-layer entities can use different syntax and semantics, as long as the presentation service understands both and the mapping between them. The presentation service data units are then encapsulated into Session Protocol data units, and moved down the stack.
This layer provides independence from differences in data representation (e.g., encryption) by translating from application to network format, and vice versa. The presentation layer works to transform data into the form that the application layer can accept. This layer formats and encrypts data to be sent across a network, providing freedom from compatibility problems. It is sometimes called the syntax layer.
The original presentation structure used the basic encoding rules of Abstract Syntax Notation One (ASN.1), with capabilities such as converting an EBCDIC-coded text file to an ASCII-coded file, or serialization of objects and other data structures from and to XML.
[edit]Layer 7: Application Layer
The application layer is the OSI layer closest to the end user, which means that both the OSI application layer and the user interact directly with the software application. This layer interacts with software applications that implement a communicating component. Such application programs fall outside the scope of the OSI model. Application layer functions typically include identifying communication partners, determining resource availability, and synchronizing communication. When identifying communication partners, the application layer determines the identity and availability of communication partners for an application with data to transmit. When determining resource availability, the application layer must decide whether sufficient network or the requested communication exist. In synchronizing communication, all communication between applications requires cooperation that is managed by the application layer. Some examples of application layer implementations include Hypertext Transfer Protocol (HTTP), File Transfer Protocol (FTP), Simple Mail Transfer Protocol (SMTP) and X.400 Mail...
[edit]Interfaces
Neither the OSI Reference Model nor OSI protocols specify any programming interfaces, other than as deliberately abstract service specifications. Protocol specifications precisely define the interfaces between different computers, but the software interfaces inside computers are implementation-specific.
For example Microsoft Windows' Winsock, and Unix's Berkeley sockets and System V Transport Layer Interface, are interfaces between applications (Layer 5 and above) and the transport (Layer 4). NDIS and ODI are interfaces between the media (Layer 2) and the network protocol (Layer 3).
Interface standards, except for the Physical Layer to media, are approximate implementations of OSI Service Specifications.
[edit]Examples
| Layer | OSI protocols | TCP/IP protocols | Signaling System 7[5] | AppleTalk | IPX | SNA | UMTS | Misc. examples |
|---|
| # | Name |
|---|
| 7 | Application | FTAM, X.400,X.500, DAP,ROSE, RTSE,ACSE | NNTP, SIP, SSI,DNS, FTP, Gopher,HTTP, NFS, NTP,DHCP, SMPP,SMTP, SNMP,Telnet, RIP, BGP | INAP,MAP,TCAP,ISUP,TUP | AFP, ZIP,RTMP,NBP | RIP,SAP | APPC | | HL7, Modbus |
| 6 | Presentation | ISO/IEC 8823, X.226, ISO/IEC 9576-1, X.236 | MIME, SSL, TLS,XDR | AFP | | | | TDI, ASCII, EBCDIC,MIDI, MPEG |
| 5 | Session | ISO/IEC 8327, X.225, ISO/IEC 9548-1, X.235 | Sockets. Session establishment inTCP, SIP, RTP | | ASP,ADSP,PAP | NWLink | DLC? | | Named pipes, NetBIOS,SAP, half duplex, full duplex, simplex, SDP,RPC |
| 4 | Transport | ISO/IEC 8073, TP0, TP1, TP2, TP3, TP4 (X.224), ISO/IEC 8602, X.234 | TCP, UDP, SCTP | | | DDP,SPX | | | NBF |
| 3 | Network | ISO/IEC 8208,X.25 (PLP), ISO/IEC 8878,X.223, ISO/IEC 8473-1, CLNP X.233. | IP, IPsec, ICMP,IGMP, OSPF | SCCP,MTP | ATP(TokenTalkorEtherTalk) | IPX | | RRC (Radio Resource Control)Packet Data Convergence Protocol (PDCP) and BMC(Broadcast/Multicast Control) | NBF, Q.931, IS-IS |
| 2 | Data Link | ISO/IEC 7666,X.25 (LAPB),Token Bus, X.222, ISO/IEC 8802-2 LLC Type 1 and 2 | PPP, SLIP, PPTP,L2TP | MTP,Q.710 | LocalTalk,AppleTalk Remote Access,PPP | IEEE 802.3framing,Ethernet II framing | SDLC | LLC (Logical Link Control), MAC(Media Access Control) | 802.3 (Ethernet),802.11a/b/g/n MAC/LLC,802.1Q (VLAN), ATM,HDP, FDDI, Fibre Channel, Frame Relay,HDLC, ISL, PPP, Q.921,Token Ring, CDP, ARP(maps layer 3 to layer 2 address), ITU-T G.hn DLL |
| 1 | Physical | X.25 (X.21bis,EIA/TIA-232,EIA/TIA-449,EIA-530,G.703) | | MTP,Q.710 | RS-232,RS-422,STP,PhoneNet | | Twinax | UMTS L1 (UMTS Physical Layer) | RS-232, Full duplex,RJ45, V.35, V.34, I.430,I.431, T1, E1, 10BASE-T,100BASE-TX, POTS,SONET, SDH, DSL,802.11a/b/g/n PHY, ITU-T G.hn PHY |
[edit]Comparison with TCP/IP
In the TCP/IP model of the Internet, protocols are deliberately not as rigidly designed into strict layers as the OSI model.[6] RFC 3439contains a section entitled "Layering considered harmful." However, TCP/IP does recognize four broad layers of functionality which are derived from the operating scope of their contained protocols, namely the scope of the software application, the end-to-end transport connection, the internetworking range, and lastly the scope of the direct links to other nodes on the local network.
Even though the concept is different than in OSI, these layers are nevertheless often compared with the OSI layering scheme in the following way: The Internet Application Layer includes the OSI Application Layer, Presentation Layer, and most of the Session Layer. Its end-to-endTransport Layer includes the graceful close function of the OSI Session Layer as well as the OSI Transport Layer. The internetworking layer (Internet Layer) is a subset of the OSI Network Layer, while the Link Layer includes the OSI Data Link and Physical Layers, as well as parts of OSI's Network Layer. These comparisons are based on the original seven-layer protocol model as defined in ISO 7498, rather than refinements in such things as the internal organization of the Network Layer document.
The presumably strict consumer/producer layering of OSI as it is usually described does not present contradictions in TCP/IP, as it is permissible that protocol usage does not follow the hierarchy implied in a layered model. Such examples exist in some routing protocols (e.g., OSPF), or in the description of tunneling protocols, which provide a Link Layer for an application, although the tunnel host protocol may well be a Transport or even an Application Layer protocol in its own right.
The TCP/IP design generally favors decisions based on simplicity, efficiency and ease of implementation.[citation needed]
[edit]See also